Hey there. New year – first article. I’d like to talk about ssh-chat by shazow/Andrey Petrov, today. “ssh-chat” is a cross-platform, very interesting instant messaging chat daemon/SSH server, written in GoLang, giving opportunity to make private and group chats with other Linux/*BSD users over SSH.
Connecting to the port it listens, instead of a shell, you get a fancy, retro, IRC-like chat prompt, with actually really cool terminal color themes! So, once we launch it, what we’ll get is a chat prompt rather than a usual shell. Therefore it enables to chat securely over an SSH connection.
Here are the details on how I installed it on my OpenBSD VPS;
(Before you go all-through, you might wish to test it; just ssh into the hostname: ssh.chat on port 22 and see how beautifully it works there!)
First step ever: Bring your Puffy some love and always syspatch it! <3
obsdbox# syspatch Get/Verify syspatch68-007_xmaplen... 100% |*************| 4547 KB 00:00 Installing patch 007_xmaplen Relinking to create unique kernel... done; reboot to load the new kernel Errata can be reviewed under /var/syspatch
Reboot the system and then install Go. Without it, ssh-chat wouldn’t build.
obsdbox# pkg_add go quirks-3.440 signed on 2020-12-29T22:36:31Z quirks-3.439->3.440: ok go-1.15.2: ok Read shared items: ok
Then, add a user called, e.g., “sshchat“, that’s because for security reasons -obviously-, you should not run ssh-chat with root.
Login with the user you created, afterwards, proceed with the following steps;
Generate ssh keys for ssh-chat:
obsdbox$ ssh-keygen -t ed25519 -a 300 -f ~/.ssh/ssh-chat-key Generating public/private ed25519 key pair. Enter passphrase (empty for no passphrase): (always give it a strong password) Enter same passphrase again: Your identification has been saved in /home/sshchat/.ssh/ssh-chat-key Your public key has been saved in /home/sshchat/.ssh/ssh-chat-key.pub The key fingerprint is: SHA256:ss33gh8DS2v1uJYJglgjkACYSlBxgYSPSGHr2wYCrJI sshchat@obsdbox The key's randomart image is: +--[ED25519 256]--+ |OO=oo. | |Ooo. | |** | |B.o o | |Eo + o. S . | |o = . .*.= o | | . o ..*o=o. | | . ...== | | oo.. | +----[SHA256]-----+
The command above will create two key files (private&public) inside the “.ssh” folder located within your user’s home folder (/home/sshchat/.ssh/)
The parameter -a 300 defines the number of rounds for the key derivation function. The higher this number, the harder it will be for someone trying to brute-force the password of your private key (well, in case of any access), but also the longer you will have to wait during the initialization of an SSH login session.
and -t parameter specifies the type of key to create. The possible values are “dsa”, “ecdsa”, “ecdsa-sk”, “ed25519“, “ed25519-sk”, or “rsa”.
I prefer Ed25519/EdDSA algorithm, because:
(1) Ed25519 is a modern and secure public-key signature algorithm, brings many performance and security features, resistance against several side-channel attacks.
(2) It provides the highest security level compared to key length. It also improves on the insecurities found in ECDSA.
(3) It is also a very fast signature algorithm, very secure, the keys and signatures a very small.
Continue with creating an empty directory for ssh-chat, and download its source files into that folder.
obsdbox$ mkdir ssh-chat obsdbox$ cd ssh-chat/ (make sure to check for the latest version on: https://github.com/shazow/ssh-chat/releases) obsdbox$ ftp https://github.com/shazow/ssh-chat/archive/v1.10.tar.gz Trying 140.82.121.4... Requesting https://github.com/shazow/ssh-chat/archive/v1.10.tar.gz Redirected to https://codeload.github.com/shazow/ssh-chat/tar.gz/v1.10 57477 bytes received in 0.00 seconds (17.95 MB/s) (Extract it) obsdbox$ tar zxf v1.10.tar.gz obsdbox$ ls -al total 128 drwxr-xr-x 3 root wheel 512 Jan 1 13:44 . drwx------ 4 root wheel 512 Jan 1 13:44 .. drwxr-xr-x 8 root wheel 1024 Aug 3 18:13 ssh-chat-1.10 -rw-r--r-- 1 root wheel 57477 Jan 1 13:44 v1.10.tar.gz (cd into the extracted folder and build it) obsdbox$ cd ssh-chat-1.10/ obsdbox$ make build go build -ldflags "-X main.Version= -extldflags "-static"" ./cmd/ssh-chat go: downloading github.com/alexcesaro/log v0.0.0-20150915221235-61e686294e58 go: downloading github.com/shazow/rateio v0.0.0-20200113175441-4461efc8bdc4 go: downloading github.com/howeyc/gopass v0.0.0-20190910152052-7cb4b85ec19c go: downloading github.com/jessevdk/go-flags v1.4.0 go: downloading golang.org/x/sys v0.0.0-20200420163511-1957bb5e6d1f go: downloading golang.org/x/text v0.3.2 go: downloading golang.org/x/crypto v0.0.0-20200420104511-884d27f42877 obsdbox$
Build is now done flawlessly. You now have ssh-chat binary in the same folder you’re in. Let’s take a look at the default output of ssh-chat.
obsdbox$ ls -Flha ssh-chat
-rwxr-xr-x 1 sshchat wheel 10.8M Jan 1 13:54 ssh-chat*
obsdbox$ ./ssh-chat --help
Usage:
ssh-chat [OPTIONS]
Application Options:
--admin= File of public keys who are admins.
--bind= Host and port to listen on. (default: 0.0.0.0:2022)
-i, --identity= Private key to identify server with. (default: ~/.ssh/id_rsa)
--log= Write chat log to this file.
--motd= Optional Message of the Day file.
--pprof= Enable pprof http server for profiling.
-v, --verbose Show verbose logging.
--version Print version and exit.
--whitelist= Optional file of public keys who are allowed to connect.
--unsafe-passphrase= Require an interactive passphrase to connect. Whitelist feature is more secure.
Help Options:
-h, --help Show this help message
Start the ssh-chat daemon (in my example; listening on 2323 port, using the ssh keys we generated earlier):
obsdbox$ ./ssh-chat --verbose --bind ":2323" --identity /home/sshchat/.ssh/ssh-chat-key Enter passphrase: (The password you gave during creating the keys) Final: Listening for connections on 0.0.0.0:2323
Yep, the server is listening now on TCP port 2323. We can test it through connecting to external IP:port, by using any ssh client. Under OpenBSD, execute:
ssh mynick@ip.add.re.ss -p 2323
Or should you wish to have a default “theme” for your terminal chat screen, feel free to issue “SSHCHAT_THEME” environmental variable within ssh command, which allows you to define what theme you would like for your session. Also enabling timestamps;
ssh -o "SetEnv SSHCHAT_THEME=hacker SSHCHAT_TIMESTAMP=1" mynick@ip.add.re.ss -p 2323
The /help command in chat window will bring you all the features as options, including list of themes and so.
How to become server Admin:
To become an Admin, I run the server with (pointing –admin to my public key file):
./ssh-chat --verbose --bind ":2323" --identity /home/sshchat/.ssh/ssh-chat-key --admin=/home/sshchat/.ssh/ssh-chat-key.pub
Then on an OpenBSD box, I connect to the server with my private key file:
ssh mynick@obsdbox -p 2323 -i /home/sshchat/.ssh/ssh-chat-key
Or under Windows, copy the content of your private key ‘/home/sshchat/.ssh/ssh-chat-key‘ file, save it as text file, load it on your ssh client as Key File, to login to chat server as admin. A Windows based telnet/ssh-client Putty handles it good, however, the key must be converted by the PuTTYgen tool.
https://ozgurkazancci.com/down/puttygen.exe
Download the utility through the website, open it, and select the “Conversions” tab in the top panel. In the menu that opens, press “Import key” and select your key file. click “Save private key.” The key will be saved in a new format (.ppk) with the selected name.
And of course, you might also wish to use Windows 10’s default ssh client in command console.
That’s all for today.
Happy New Year!
Project link: https://github.com/shazow/ssh-chat
Fully-detailed Project blog: https://shazow.net/posts/ssh-how-does-it-even/
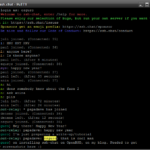
Some screenshots:

![Validate my RSS feed [Valid RSS]](/valid-rss.png)